Accessing HG8245Q Shell: in this article, you will learn how to access HG8245Q shell through Telnet, using default credentials, and how to solve the challenge for SU password using a simple Python script.
HG8245Q Home Router
This is a short story, about accessing HG8245Q shell through Telnet, the whole process took me less than 15 minutes to finish.
In this article, I will show you how to:
- Scan for open ports using nmap (searching for telnet).
- Connect to the CLI via telnet, using default credentials.
- Access the configuration mode, and solve the challenge string.
- Access the shell of the router.
Note: the time on the snapshots in this article, is not accurate, so please ignore it.
Scanning and Discovery
To get the gateway IP address, you can use the IPCONFIG command, or ifconfig command in care you are using Linux/Unix, the snapshot above illustrates my results.
Once you get the gateway IP address, you can scan for open ports, I recommend using nmap (TCP/first 1000 ports), where -sT option is for TCP port scanning, and -T5 option means insane (fast) scan, we don’t care about the traffic or being detected, once the scan is finished, you should see that port 23 was open.
Solving the Telnet Riddle
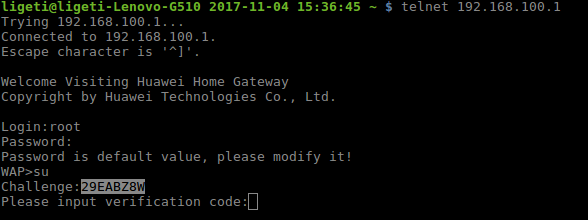
Use telnet command to connect to the AP, you should see a banner that reads: “Welcome Visiting Huawei Home Gateway”, I believe that it would be really rude not to enter, especially after this generous invitation, we don’t want to be rude now, do we?
However, we need the credentials, so let’s try the default username and password, which is very easy to guess, and you can even search for it online.
Username: root
Password: admin
Once you are logged in, you can list all the available command by using the ‘/?’ Command, you will find two commands that are interesting: su and shell.
Now, to become su, you be asked to solve a challenge string, I didn’t know the algorithm, so I searched for the frameware first, thinking that I may be able to find it there, but instead, I found a script on GitHub: https://github.com/abrdiaz/router-scripts/blob/master/huawei/gpons/hgsupass.py, that you will need to solve the challenge and eventually, accessing HG8245Q shell.
Solving the SU Challenge
To get the challenge string, use the su command, as shown in the snapshot below.
Copy the challenge string, and solve it using the python script, as shown in the snapshot below, and this is it, you should be in now.
Accessing HG8245Q Shell
The rest is easy, all you need to do is to issue the shell command and voila, access granted.
Now, you should notice that BusyBox/Shell commands are disabled, there are only two “useless” scripts, that I didn’t have time to be interested in them, but I believe that it is critical enough to be in the configuration mode, because you can gain total control of the AP , just check the commands and use your imagination.
Conclusion
Accessing HG8245Q shell not magic, nevertheless, I don’t think that the above is an effective exploit/attack, I was just exploring, and I didn’t try to tamper with the configuration or anything, the point is, you should never trust your ISP, and don’t trust any vendors, to secure your network, you must check the configuration, and believe me, I found many back-doors, and security flaws in home devices and IoT, so many, that I am utterly and ridiculously bored.
Finally, don’t forget to share your thoughts with us, so please leave your comments or questions if you have any, and I will try my best to answer them as soon as possible.
Thanks.





Pingback: Hg8546m Default Login - Loginplug.com
hepl plz @@
WAP>set suadmin on Securekey:C505AF1C45FA68863F665D0A1501C000
I successfully login to shell and get this:
WAP>shell
BusyBox v1.18.4 (2017-12-26 17:06:34 CST) built-in shell (ash)
Enter ‘help’ for a list of built-in commands.
can’t get to the damn file to crack my web access password (alas, none of the defaults work).
Any help would be appreciated.
Thank you for sharing this with us, really useful/interesting to know, I should give it a try soon.
i did this:
connect by telnet…no challenge for me…maybe lucky
telnet root admin
then copied hw_ctree.xml from directory to usb( 2 ports has mine)…
you can find in /mnt/jffs2/hw_ctree.xml
just cp /mnt/jffs2/hw_ctree.xml /usb.1_1/ something like this
and VOILA file in usb….then all process with aescrypt2 ( dont forget to change user level to 0 and then copy again from usb to router
cp /usb.1_1/hw_ctree.xml /mnt/jffs2/
Ok???
i have now full access router with user
‘/?’ doesnt work
shell give nothing
su ???
Hi, my ISP has blocked my access to this router by forwarding the ip into their so called app which only allows to change the SSID and Password…
I tried resetting my router from outside, but it somehow retains its current state( same SSID & PW)
.
.
Is there a way to solve this problem..?
found it on reddit. its adminHW
For Batelco I tried and it didn’t work. do you have any other suggestions?
For Batelco I tried and it didn’t work. do you have any other suggestions?
hi how to generate ssh-keygen on that shell router?
for Bahrain Batelco Provider, the default password for all routers are root/adminHQ
I cannot solve the challenge to access the shell. Can you help me?
After running the script, I got blank answers.
Unfortunately default user and pass for telnet did not work for me!
Is there a way to change/reset them?
So what’s the general direction of “complete control of the AP”? My imagination must be a bit limited 🙂
Interesting, please let me know how it goes, I am really interested to know, and good luck.
Thank you for the reply,
As of now I’m trying to access via serial console, but the pins are disabled. In the next days I’ll manage to solder the necessary resistence to try accessing
Hello Paolo
I got the same results (I think I mentioned that in my post), but to be honest, I didn’t get a chance to go any further as I didn’t have enough time to explore, I don’t have access to HG8245Q right now, so I can’t really help much with that.
I don’t think that your goal is easy to achieve, unless you find another way to get in (backdoor, or a web-shell maybe), not from Telnet/shell as there are not much you can do there, I am most probably wrong, because, and again, I didn’t have enough time to explore.
Hi
I have a HG8245q that seems to be factory unlocked. I mean: I had the access to root telnet busybox shell (with only exit and getcustominfo.sh) without doing the challenge unlock.
As of now, the busybox cli has only these 2 commands, but I need to find the voip plaintext password provided via tr-069 from my provider.
From the downloaded hw_ctree.xml file (unencrypted by default) all the passwords are encoded in a “$1[24char]$” format that seems to be like AES-256-CBC encryption.
Do you know how to see the plaintext passwords inside the NVRAM or maybe how to escape from the limited busybox of this router?
Thank you
Hello… Thanks alot for this writeup. I was struggling to get some access to my ONT for last 2 days and finally I am in the shell. I have a IT background but not of networking and am good at unix, so feels fine now.
My problem is that I was not able to login to the ONT (Huawei HG8546M) after my provider did a factory reset. Now that I am in the shell, can you guide me further? I will explore the files in the shell, but your response will be quick solution for me. I have already asked for a new ONT. If this gets working I can save some bucks!
Thanks again.
How to use phyton code to solve challange?
I’m sorry, I’m confused eheh
ED! I am speechless indeed, this is nothing compared of what we did in the old days, wow! Just thinking about how long has it been makes me feel really dizzy! I hope history will repeat itself one day soon, I miss that spirit we had, but I still have faith.
Thank you, you can’t imagine how happy I am to see you here 🙂
Following another classic maneuver adeptly executed by the infamous Ligeti, a yawn like that of a great, mighty champion escapes the legend as he gazes into the horizon and ponders the challenges that lay beyond.